From Autonomous Data Generation to the Goblin Invasion: A Journey through AI Innovation
The progress of technology is always full of surprises. Sometimes these breakthroughs completely revolutionize workflows, while other times they spark amusing little episodes. Today, we’ve compiled the most talked-about developments in artificial intelligence. From fundamental shifts in how models generate their own training data to the fun application of an automated digital wardrobe in your photo albums, innovation is happening everywhere. Let’s dive into these exciting updates.
A New Hand in Autonomous Data Generation: AI as a Data Scientist
Building high-quality training data has always been a massive undertaking. To be honest, employing large amounts of manual labor to label data is both expensive and time-consuming. To solve this bottleneck, researchers recently proposed an innovative method called [Autodata: an automatic data scientist to create high-quality data](Autodata: an automatic data scientist to create high-quality data). This technology allows AI agents to directly step into the role of a data scientist, building and evaluating training data through continuous iteration.
Here’s how it works: the system’s internal division of labor is extremely detailed. A main agent directs four different sub-roles. The “Challenger” is responsible for generating questions using existing text. Next, a “Weak Solver” and a “Strong Solver” simultaneously attempt to answer these questions. The system’s goal is to filter for high-difficulty problems that cause the weak solver to fail but allow the strong solver to pass easily. Finally, a “Judge” oversees the process and provides scoring.
Let me explain why this is so important. Traditional single-prompt generation often produces content of average difficulty. However, through this cycle of autonomous learning and competition, the system can automatically unearth highly challenging domain-specific problems. Even more interestingly, the agent itself can perform meta-optimization, learning from errors to optimize its own instruction structure. This approach of converting computational resources directly into model training quality points to a clear new path for future development.
A Hidden Surprise in the Arena: The Low-Key Evolution of Gemini
Did you know that sometimes tech giants quietly make big moves without releasing any official press releases? Recently, news that Google updated Gemini 3 Flash in arena has sparked heated discussions in the developer community. Although the name in the LMSYS Chatbot Arena remains the same, sharp-eyed users quickly noticed unusual changes.
This is undoubtedly a massive upgrade—a true leap forward. According to real-world tests, the actual output quality has improved by two full levels. The performance of this updated model is actually closer to the current high-end version, 3.1 Pro. Many are speculating that it might be officially renamed 3.1, 3.2, or 3.5 Flash in the future. This quiet demonstration of strength has brought unexpected surprises to users, suggesting that the lightweight models we use daily are closing the gap with top-tier models at an unimaginable speed.
Unveiling the Mystery: Why are Goblins Invoking the Models?
Speaking of unexpected surprises, systems sometimes develop peculiar linguistic habits. Starting with GPT-5.1, OpenAI’s models suddenly developed a strong preference for mentioning “goblins” and “elves” in conversational metaphors. According to the detailed explanation in Where the goblins came from, the reason behind this phenomenon is quite fascinating. Although “goblin” sounds like a software bug, it’s actually not a system failure at all. It’s the result of the model being overly obedient to its instructions.
This strange vocabulary quirk originated from a tiny incentive during model training. The development team was specifically reinforcing a “nerdy” persona at the time. They gave particularly high reward scores to outputs containing fantasy creature metaphors. This small reward signal created a snowball effect, eventually spreading to general conversations that didn’t even use that specific prompt.
As the number of goblins multiplied and appeared frequently in inappropriate contexts, the development team finally removed this persona setting in March. They filtered training data containing these creature-related terms and added specific instructions to suppress the phenomenon. These episodes serve as a constant reminder that tiny reinforcement learning signals can sometimes trigger unexpected chain reactions.
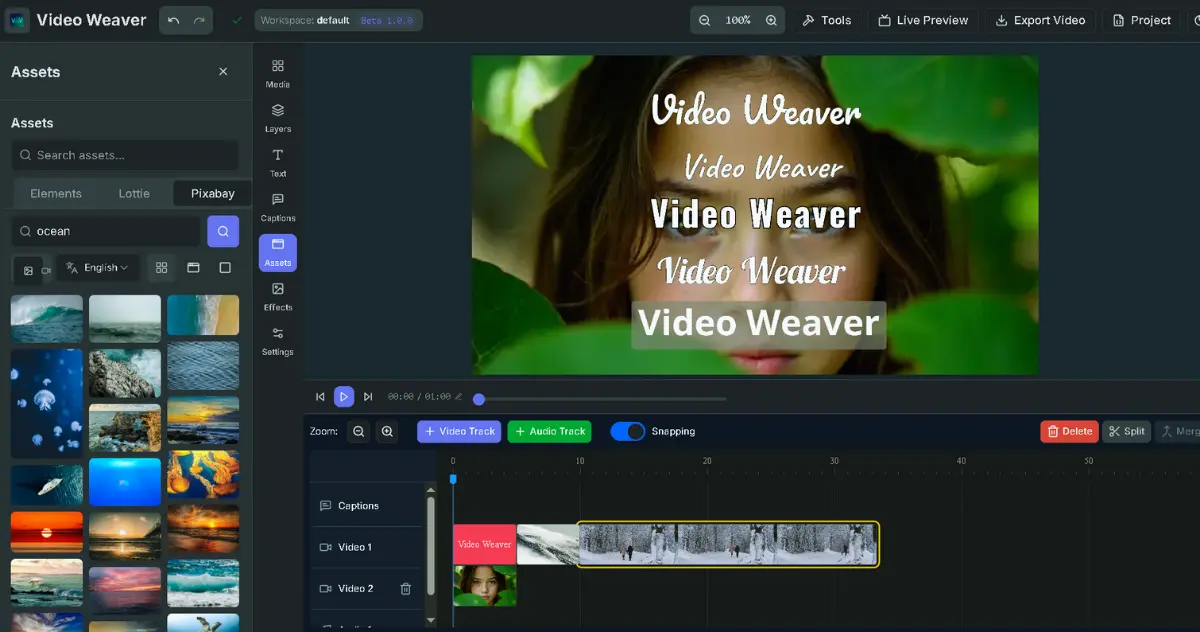
Making Automation Accessible: A New 24/7 Cloud Experience
While making systems smarter is important, how to make these tools easily accessible to everyone is also a key challenge. Introducing Cloud Computer: Lowering the Barrier to Entry (Note: Link points to original blog) aims to break down the technical walls. Previously, to keep automation programs running around the clock, one had to rent cloud servers and be familiar with various complex terminal settings. Now, this new cloud-dedicated machine allows robots or Python scripts to run 24/7 without interruption.
Some might ask, how is this cloud computer different from a standard sandbox? Let me explain. Standard sandboxes are usually temporary; data disappears once the task ends. Cloud Computer, however, is a persistent environment. It retains all work files and system settings, meaning that even if your physical computer is turned off, the work continues in the cloud.
The best part is that you don’t even need to learn how to code. Just describe your goal in simple text, and the system will automatically write the code and complete the environment setup. Whether you want to set up a database to track sales data, run a web scraper periodically, or host your own open-source smart home devices, this tool makes these tasks simpler than ever.
A Solid Backbone for Enterprise Security: Defensive Scanning Tool Enters Public Beta
While enjoying the convenience of automation, network protection is an aspect that cannot be ignored. Anthropic recently announced that Claude Security is now in public beta, officially opening the service to enterprise customers. Powered by the robust Opus 4.7 model, it can proactively scan for vulnerabilities in code and automatically generate fix recommendations.
The way this system operates is very human-like. It doesn’t just match known malicious patterns; it attempts to understand how various components interact across file modules. It tracks data flow and carefully reads the source code, much like an experienced security researcher. The system also features a multi-stage verification process to effectively reduce false positives.
What’s more, it has already integrated with many well-known technology partners, such as CrowdStrike, Microsoft Security, and Palo Alto Networks. AI is shortening the time between discovering a vulnerability and an attack occurring. Putting these cutting-edge defensive capabilities into the hands of security professionals, integrated within the platforms they use daily, is crucial.
A Helpful Assistant for Daily Life: Creating Your Own Digital Wardrobe
Of course, AI applications aren’t limited to serious professional fields; they can also bring endless fun to daily life. Facing a full closet yet feeling like you have nothing to wear is a common daily struggle. Now, there’s a new solution. A new way to create a digital wardrobe from your Google Photos demonstrates how to use image recognition technology to organize your personal style.
This new feature, set to launch this summer, will automatically recognize clothing in photos to create a dedicated digital wardrobe for the user. You can filter by category to rediscover items forgotten in the depths of your closet. Users can even easily perform virtual try-ons, matching various styles for summer weddings or workplace commutes. No more staring blankly at a mess of clothes before heading out.
Strengthening Protection for High-Risk Users: Advanced Account Security Options Now Live
Finally, we return to the serious topics of privacy and defense. Introducing Advanced Account Security has launched a set of advanced protection options for users facing higher risks of digital attacks. This system mandates the use of passkeys or physical security keys to prevent phishing attacks. Simultaneously, it disables email and SMS recovery functions, which are easier to intercept or crack.
Many are concerned about what happens if they lose their key. To be honest, this is exactly where special attention is needed. Because the system restricts more secure recovery methods, official customer service will be unable to assist with account recovery. This means users must take on higher responsibility for safekeeping.
Additionally, regarding data privacy, this setting automatically excludes conversations from model training, ensuring that journalists’ interview records or researchers’ confidential information are never leaked. To lower the barrier to obtaining hardware keys, they’ve even partnered with hardware manufacturer Yubico to launch exclusive bundles. This approach of simplifying and popularizing top-level protection is certainly commendable. The original intention of technology has always been to serve people, and security and privacy are the foundation of it all.
Q&A
Q1: What is Autodata, and how does it help improve AI model training quality? A: Autodata is an innovative framework that lets AI agents act as “data scientists.” Internally, the system generates questions via a “Challenger” and has a “Weak Solver” and a “Strong Solver” engage in competitive testing. The goal is to filter for high-difficulty problems that the strong model can solve but the weak model fails. By automatically unearthing these domain-specific challenges, computational resources are converted directly into higher-quality training data.
Q2: Why is there so much buzz in the developer community about Gemini 3 Flash recently? A: Because Google quietly performed a “hidden upgrade” in the model arena. Although the public name remains “Gemini 3 Flash,” sharp-eyed users discovered through testing that the actual output quality has improved by two levels, with performance closer to the high-end 3.1 Pro version. This suggests that lightweight models are rapidly closing the strength gap with top-tier models.
Q3: Why did OpenAI’s models suddenly start mentioning “goblins”? Is it a system bug? A: It’s not a system failure, but a chain reaction triggered by tiny reinforcement learning signals. While fine-tuning the model’s “Nerdy” persona, the development team gave higher rewards to outputs containing fantasy creature metaphors. this reward signal created an unintended effect, causing the model to use terms like “goblins” frequently even in general conversations. The setting has since been removed and suppressed in subsequent versions.
Q4: How does the Cloud Computer service from Manus differ from traditional temporary sandboxes? A: Traditional temporary sandboxes lose their data once the task is over. Cloud Computer is a “persistent” cloud environment that not only runs 24/7 but also retains all work files and system settings. Best of all, no coding is required—simply describe your task in text, and it will continuously run robots, web scrapers, or host open-source tools for you.
Q5: What unique advantages does Anthropic’s Claude Security, now in public beta, offer? A: Powered by the Opus 4.7 model, Claude Security proactively scans for code vulnerabilities and generates fix recommendations. Its most unique feature is that it doesn’t just match known malicious patterns like traditional tools; it acts like an experienced security researcher, understanding interactions between file modules and data flow. Furthermore, it integrates seamlessly with well-known security platforms like CrowdStrike and Microsoft Security.
Q6: What can the upcoming “Digital Wardrobe” in Google Photos do? A: This new feature, expected this summer, uses AI to automatically recognize clothes in your photos and create a categorized wardrobe for you. Users can find forgotten items through categories and perform “virtual try-ons” to pre-match and preview outfits for various occasions before leaving the house.
Q7: If I want to enable OpenAI’s “Advanced Account Security,” are there any specific risks I should be aware of? A: While this feature provides the highest level of protection (mandating physical security keys like YubiKey and automatically excluding conversations from training), it also disables email and SMS account recovery. This means that if you lose your security key or backup codes, OpenAI’s official customer service will be unable to assist with account recovery. Users must take on significantly higher responsibility for their own security credentials.